Project 01
Security Knowledge Graph
Flat security lists break under pressure. This graph connects people, systems, code, and business risk so decisions come from context instead of guesswork.
In Plain English
When an alert fires, you can instantly see who owns it, what it touches, and how important it is to the business.
Problem
Stale inventories and disconnected tools.
Approach
Model relationships as nodes and edges.
Result
One query answers cross-system risk fast.
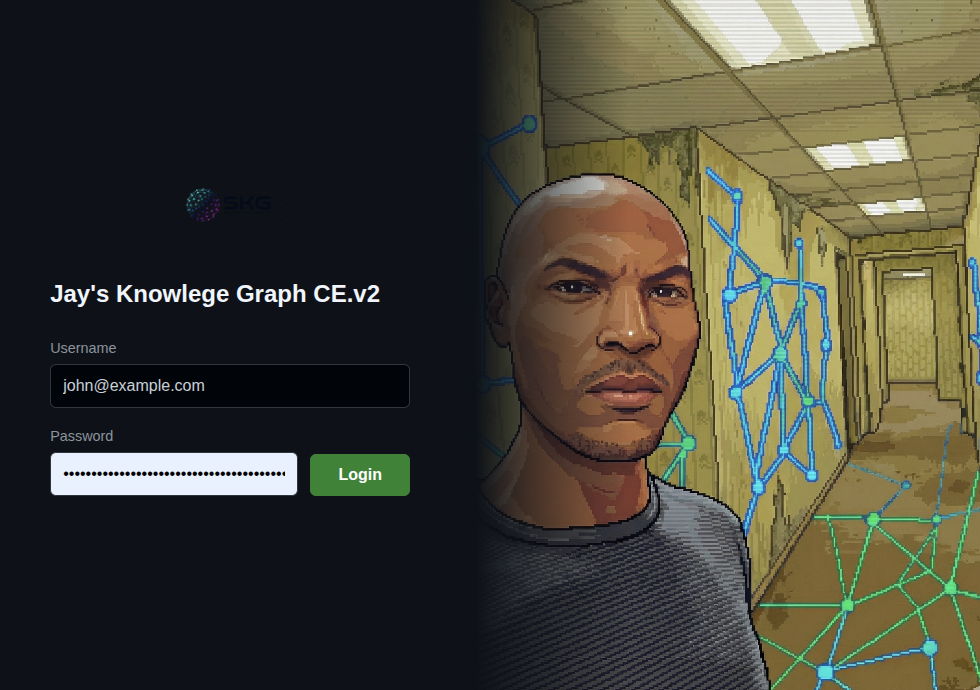
SKG Front Door: real-time ownership and risk map
Example Query
SHOW public_servers
WHERE vulnerable_to = "Log4j"
AND owner.status = "terminated"
AND owner.last_day <= NOW() - 30d
RETURN server_id, owner.name, business_unit, service_name;Before vs After
Before
Multiple stale exports, no consistent owner context.
After
Single relationship map with actionable owner and dependency links.